Blockchain forensics firm CipherTrace has published a detailed analysis of how two Chinese nationals, linked to North Korea, laundered tens of millions of dollars worth of stolen cryptocurrency.
The pair are believed to be associated with the shadowy Lazarus Group, which was behind the Sony breach in 2014, the WannaCry ransomware epidemic in 2017, and a $7 million attack on Bithumb (also in 2017).
They used ‘peel chains’ to hide the size of deposits to avoid unwanted attention, and doctored photographs to fool KYC verification processes, among other tricks.
On March 2, the United States Treasury’s Office of Foreign Assets Control (OFAC) added Tian Yinyin and Li Jiadong to its list of sanctioned individuals and entities for their involvement in laundering crypto assets stolen from an unnamed South Korean exchange in 2018. The pair have been charged with money laundering conspiracy and operating an unlicensed money transmitting business.
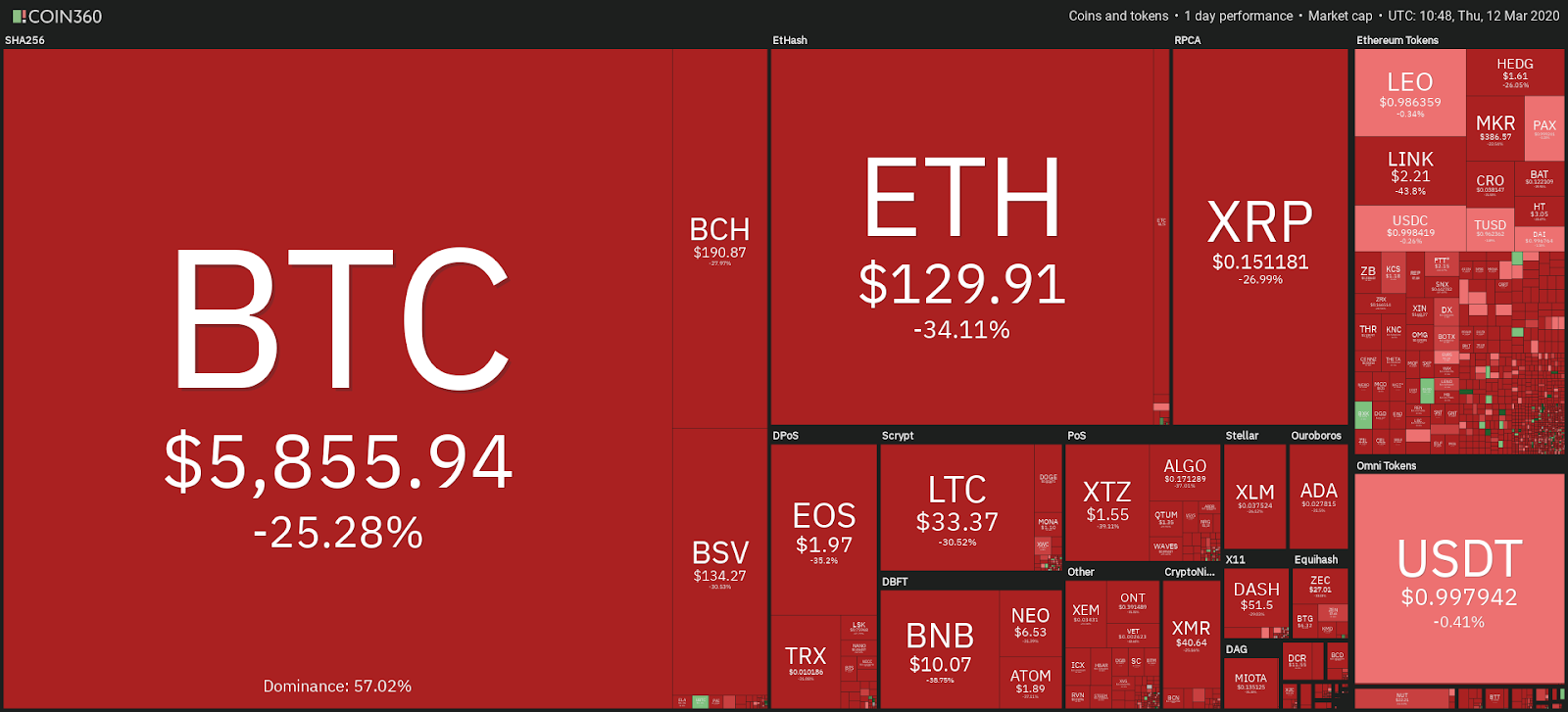
$234 million worth of crypto assets was stolen from the exchange — including 218,800 Ether worth $141 million, 10,800 Bitcoin worth $95 million, and between half a million and $3.2 million worth of Ethereum Classic, Ripple, Litecoin, Zcash, and Dogecoin.
‘Peel chains’ used to hide large deposits
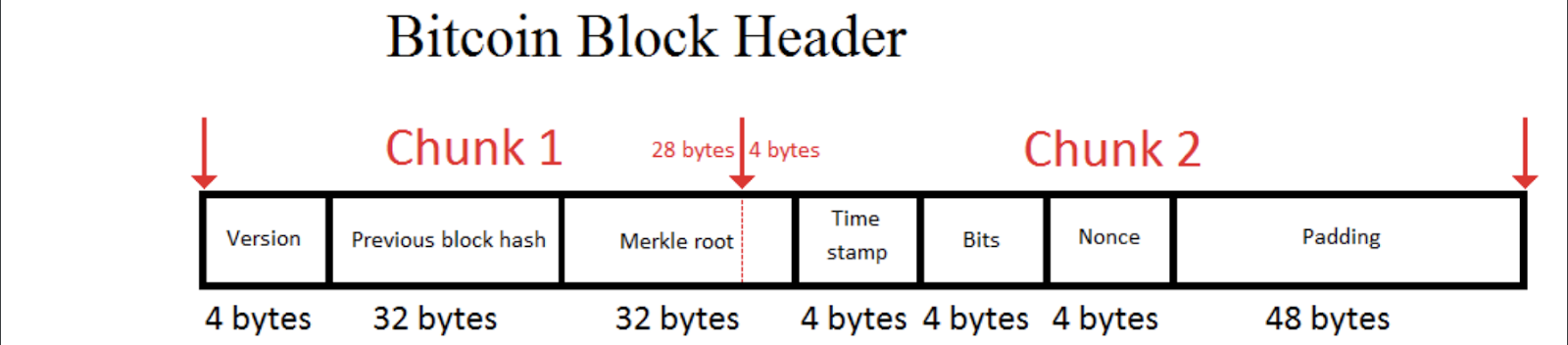
According to CipherTrace, the cybercriminals made use of “peel chains” to obfuscate the size of funds being deposited to any given wallet. Rather than attempt to make a single, large deposit to an exchange and attract unwanted attention, the criminals established a chain of addresses the stolen cryptocurrency could pass through, with a small sum of crypto being forwarded to the exchange at each juncture.
Once the capital had flowed through the peel chain via 146 separate transactions, the funds were then reconstituted on just two exchanges (again unnamed).
U.S. Treasury documents estimate that $100.5 million in stolen crypto assets flowed through Tian and Li via numerous North Korean crypto wallets. Tian moved more than $34 million from his bank account to a single exchange, while Li used nine different banks to funnel $33 million.
Further investigations revealed that the pair also used peel chains to successfully launder funds garnered through two other exchange hacks believed to be perpetrated by North Korea.
The methods used show gaping holes in KYC processes
Tian and Li were easily able to game the Know-Your-Customer (KYC) processes implemented by exchanges. The pair uploaded images to one exchange purportedly showing a South Korean man and a German man holding up government-issued IDs. The images’ metadata reveals that not only were the pictures doctored, but actually featured different heads photoshopped on the same body.
Another exchange with better security flagged images submitted by the pair as having been doctored and requested a video conference to confirm the account holders’ identities. This ended that particular KYC attempt.
In a press release announcing the charges against the Chinese nationals, General Benczkowski of the U.S. Department of Justice (DoJ) asserted that the DOJ “will pierce the veil of anonymity provided by cryptocurrencies to hold criminals accountable, no matter where they are located.”
Last month, a report concluded that North Korean internet usage had trebled over three years amid increasing cryptocurrency adoption by the regime.


 加载中,请稍侯......
加载中,请稍侯......
Comments